Discover a Technology-Forward Physical Security Solution
Cloud technology enables an integrated, scalable, mobile-ready security platform
The Cloud Won. Now What?
SaaS market penetration in security is around 20% and growing (source IHS Markit), which is steadily reducing the need for on-prem, client-server security systems.
By delivering operational benefits like secure system hosting, built-in redundancy and automatic updates, and the added convenience of simple browser and mobile applications, the cloud is the right choice in security platforms for today and tomorrow. Ready to learn more? Read our guide for more details on cloud-based security.
73% of organizations say nearly all (80%+) of their apps will be SaaS this year.
Use Actionable Insights to Improve Access and Intrusion Control
How are you using the data from your physical security system?
The Challenge
Brivo’s recent industry survey showed over 80% of respondents look at physical security data, but 67% say they cannot effectively use the data to or improve security. Businesses are not getting the complete picture of their access events or video and intrusion data. That means they cannot take actionable steps to understand trends, investigate patterns or adjust security policies.
The Solution
The level of connectivity between today’s devices and systems means more opportunities to generate actionable data that can lead to insights.
With a data-driven security platform, you can visualize your data for a unique view of your security needs. Business intelligence and machine learning within the cloud security platform can help you solve some of your biggest security challenges like meeting compliance and preventing security breaches.
The Impact
| How do daily security patterns compare across my facilities? | |
| What signals precede an actionable security event? | |
| Where are administrative privileges changed most often? | |
| Which locations stand out this week? This month? Every month? | |
| How does my physical security data correlate with other data sources? |
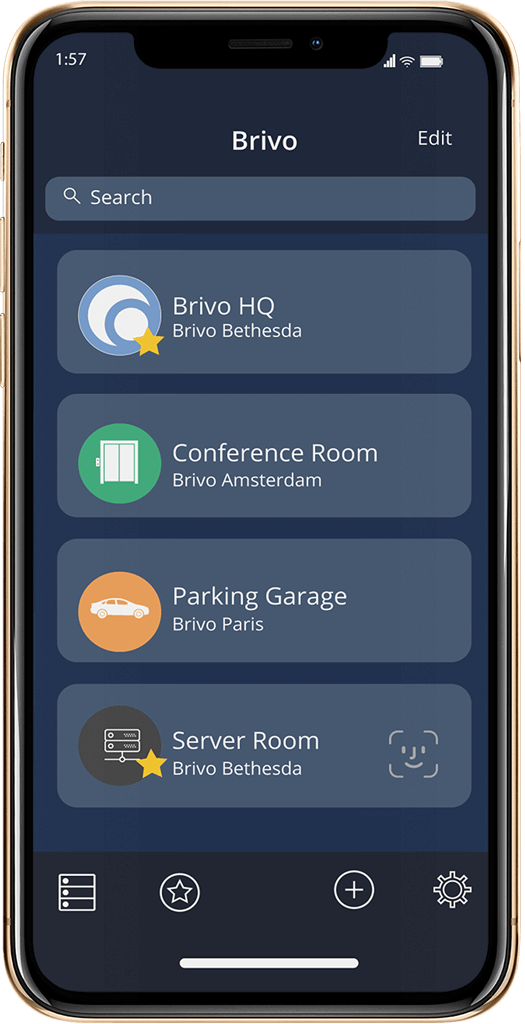
Go Mobile for Better Management and User Convenience
The Challenge
The Solution
Evaluate the mobile readiness of your security infrastructure and take steps to move to mobile credentials.
The cloud unleashes the power of mobility for both end users and security system administrators. The use of wireless technology for remote centralized security management and mobile credentials not only opens doors, it opens the opportunity to create the connected ecosystem you need to grow your business.
Mobile credentials have an overall adoption rate at around 25% (source Security Magazine). A mobile-enabled physical security solution does much more than secure the premises: it drives efficiency and provides another source of data to generate further security insights.
The key is making sure that your mobile access integrates with complementary business applications for a seamless user experience.
The Impact
Meet your business goals with mobile solutions that allow you to:
| Manage your facilities any time, without being physically onsite | |
| Assign mobile credentials to authorized employees, contractors or visitors with the click of a button | |
| Save time replacing lost or forgotten access cards | |
| Quickly ramp up new locations with limited requirements for on-premise staff | |
| Reduce security breaches with a secure, encrypted credential that can’t be cloned |
Is your business using mobile credentials to manage your building(s) from anywhere
Ensure Physical Security and Identity Management Solutions Are Aligned
How are you managing user access to buildings and access to business software and tools?
The Challenge
Identity and access management (IAM) challenges are compounded when administrators are required to use multiple systems to ensure the right individuals have access to the right resources at the right times. IT departments use IAM tools like G Suite, Okta and Azure to centrally control employee access to web services, while security managers use dedicated security systems to manage building access. This disconnect can lead to mistakes, productivity delays and security breaches.
The Solution
Integrate physical security and identity management systems so you can easily provision and deprovision users.
Integrating IAM and physical security means any changes in your IAM tool automatically update to an employee’s physical security permission. This synchronization eliminates worry that inactive users can enter your building or access business applications. By integrating these cross-functional solutions, you can deliver better security with less work and ensure users access rights are always up to date
The Impact
Make physical security part of your identity management network to:
| Quickly identify authorized users and reliably de-provision users to remove access | |
|
Manage users from one system and eliminate duplicative data entry for new or modified request access |
|
|
Reduce auditing and compliance work |
|
| Ensure the right users always have the correct level of access to your facilities |
Create a Welcoming and Safe Visitor Experience
The Challenge
The Solution
Own your visitor experience by making visitor registration and management part of your physical security platform.
Every time a visitor enters your building, you are making a first impression. You’re also protecting your employees/tenants. Your sign-in experience should be fast and simple but also meet security protocols.
No check-in staff? No problem.Give visitors the option to directly interact with a check-in kiosk where they can quickly input their name, take a picture for their temporary badge and select their host from your employee/tenant list. This makes check-in easy and convenient for them while your access control automations run in the background to ensure the visit is properly tracked for security reasons.
Creating a unified solution also solves a pain point that stand-alone systems cannot address: data integration with your core security systems. Bringing together security and cross-functional systems leads to digital transformation to improve your business while transforming security.
The Impact
Improve your visitor experience by implementing better security that:
| Automates the sign-in experience to create a welcoming, secure and convenient first impression | |
| Simplifies the process of notifying hosts when their visitors arrive | |
| Prints visitor badges that clearly display visitor identification | |
| Asks customized questions during sign-in (such as if the visitor has experienced recent illness) to protect all building occupants | |
| Allows you to customize workflows for visitor needs during the registration process |
How does visitor management fit into your security technology portfolio?
Bringing It All Together
Why Brivo
Brivo is a simply better security solution that integrates with your business ecosystem to transform how you protect people, properties and assets. Our platform balances security with modern convenience while bringing you data intelligence, mobile readiness, and scalability. Improve your organization’s security and IT strategies with Brivo.
The Brivo platform brings you:
Remote management to oversee security from any mobile device
Mobile credentials to open doors with your smartphone
Lockdown controls to quickly and effectively secure the building
Visitor management to improve guest registration experience
Identity management to better control user access permission
Easy-to-understand analytics for reporting and security policy improvements
Expand your physical security benefits with the Brivo API.
Identity management
Visitor management
Intrusion control
Elevator control
Learn how our integrations help you achieve better security with less work to create an ecosystem of building automation solutions.